It is possible to network Windows servers via the DCOM interfaces. These interfaces operate with a complicated security system. This security barrier is too complex for many users, which is why they often do without the Microsoft security concept. Microsoft will now prevent this waiver and makes its security systems mandatory for the application. This tightening of security measures is called DCOM Hardening. Read more in our article about what you need to know about the topic and what you should pay attention to before March 14, 2023.
What is DCOM?
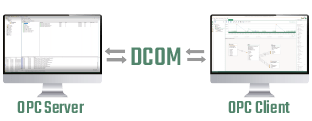
DCOM stands for Distributed Component Object Model and represents the interfaces in internal company communication. By using DCOM, servers and clients can communicate in their company-internal network. In doing so, DCOM provides an interface for software which ensures that different components are connected. DCOM uses the TCP security protocol.
DCOM in practice
In practice, the encryption and security concept around DCOM is not frequently used. Since the security principle of DCOM is complicated, cumbersome and thus difficult to implement, some companies refrain from using it. In the settings of DCOM, it is possible to make changes in such a way that the security barrier is bypassed. To secure internal communication, these companies rely on encryption for external access and thus try to protect their system landscape from unauthorized access.
DCOM Hardening
Since many companies circumvent Microsoft’s DCOM security concept, the corporation is currently planning to prevent this from a technical point of view. Microsoft will introduce DCOM Hardening with the upcoming update on March 14, 2023. Starting with this update, Microsoft will prohibit the disabling and bypassing of the DCOM security concept, thus obliging users to meet the security criteria.
Those users who do not adjust their DCOM settings before the update in March will then face a connection problem. After the update, connections that do not meet the DCOM security precautions will be blocked. Thus, internal communication will fail immediately.
Therefore, we strongly recommend switching the communication to OPC UA or complying with Microsoft’s security measures to continue using OPC DA (Classic).
Which customers will be affected?
DCOM Hardening mainly affects customers who use OPC DA (Classic) on a Windows server. OPC DA (Classic) uses the Microsoft technologies COM and DCOM and is therefore no longer usable after the Windows update. Many OPC servers are still running with OPC DA (Classic) today.
What are the alternatives?
DCOM
One way to ensure your internal corporate communications continue is to comply with Microsoft’s security precautions. However, we recommend that you take care of Microsoft’s conditions in time so that your communications do not fail after the update on March 14.
OPC UA
An alternative to DCOM is OPC UA (OPC Unified Architecture). With its platform independence and interoperability, the successor to the OPC standard OPC DA offers a viable alternative to OPC Classic and DCOM.
OPC UA was developed to be “firewall-friendly” and can thus be controlled and managed via standard network techniques. Multiple security protocols and certificate exchanges with each OPC client ensure secure communication and smooth data transfer.
Tunneling
To replace communication via DCOM technology, some software manufacturers have created Tunneling. With Tunneling, data is converted into a simple TCP/IP and thus encrypted and routed past the firewall. The data is unpacked again in the target network and provided to the OPC server. This solution can replace the DCOM and is an alternative to your DCOM encryption. If you are already using OPC UA, Tunneling is no longer necessary.
Further information
In our step-by-step instructions, you will find everything you need to know about connecting your cloud alternative to the OPC Router.
OPC UA stands for Open Platform Communications Unified Architecture and is one of the most prominent communication standards in the IoT. OPC UA enables standardized access to machines, devices and other systems. In our article: “What is OPC UA?” you will learn everything you need to know about OPC UA.
The OPC UA Client Plug-in of the OPC Router can read and write data from OPC servers. That allows the coupling of different systems with relevant data. See if the OPC UA Client Plug-in is right for your use case.
An OPC server with existing security and without DCOM? Take a closer look at the Kepware OPC Server. It acts with its security systems and offers an alternative for your OPC data.